LWE to RLWE Conversion
Continuation into LWE to RLWE conversion.
This article builds on the LWE to LWE Key Switching. Read it first before proceeding with this one.
Here, we introduce the concept of converting LWE to RLWE ciphertexts which is the second contribution of the CDKS paper.
It is helpful to convert between the different encryption schemes since:
- LWE is simpler and works well for lightweight encryption.
- RLWE is more efficient for complex homomorphic computations. RLWE can leverage NTT-accelerated multiplication to achieve faster operations
In the previous article, we introduced polynomial embedding, which allows us to convert LWE into a valid RLWE ciphertext. As noted, the embedding produces a polynomial with correct constant term but garbage elsewhere. To make this a valid RLWE encryption of the scalar message , we must zero out the non-constant coefficients.
The mathematical tool that accomplishes this is called the Field Trace.
Field Trace
Field trace is a mathematical "filter" that zeroes out all non-constant terms while retaining the constant. This is exactly what we need to cancel out the garbage in the embedded RLWE ciphertext.
Here, denotes the rational numbers and is the cyclotomic field — the number field in which our RLWE polynomials live. The details are not important for intuitive understanding but can be found in the original paper.
But how does the field trace achieve this filtering effect? The answer lies in the concept of Symmetrization.
Symmetrization
Symmetrization relies on two fundamental concepts:
- Invariance (things that stay the same)
- Cancellation (things that balance out)
In the context of a polynomial:
- The constant term (a simple integer) looks the same from every view. It is invariant.
- The variable terms () change with every view.
Mathematically, these different "views" come from the Galois group — automorphisms that rotate the root of unity (represented by ) to other valid roots. But the intuition is simpler:
Think of each automorphism as looking at the polynomial from a different, symmetric angle.
- The Constant Term (): This is a simple integer. It is invariant. No matter how you "rotate" the coordinate system (), an integer like remains .
- The Variable Terms (): These depend on . When you apply an automorphism, these terms rotate to point in different directions in the complex plane.
When you sum them all up, the invariant parts (constants) add up constructively, while the variable parts cancel each other out (destructive interference).
The Field Trace is the sum of all these different views. When you perform this summation, two distinct physical-like phenomena occur:
- Constructive Interference (The Message) Since the constant term is invariant, it looks exactly the same in every view.
- If you have views, and in every view the value is , the sum is simply:
The signal reinforces itself.
- Destructive Interference (The Garbage) The variable terms are roots of unity. A key property of these roots is that they are perfectly distributed around the unit circle (see visuals below).
- For every view where a term is positive, there is a symmetric view where it is negative.
- For every vector pointing "up," there is one pointing "down."
- When you sum all these symmetric vectors together, they perfectly balance each other out to zero.
Visual Intuition
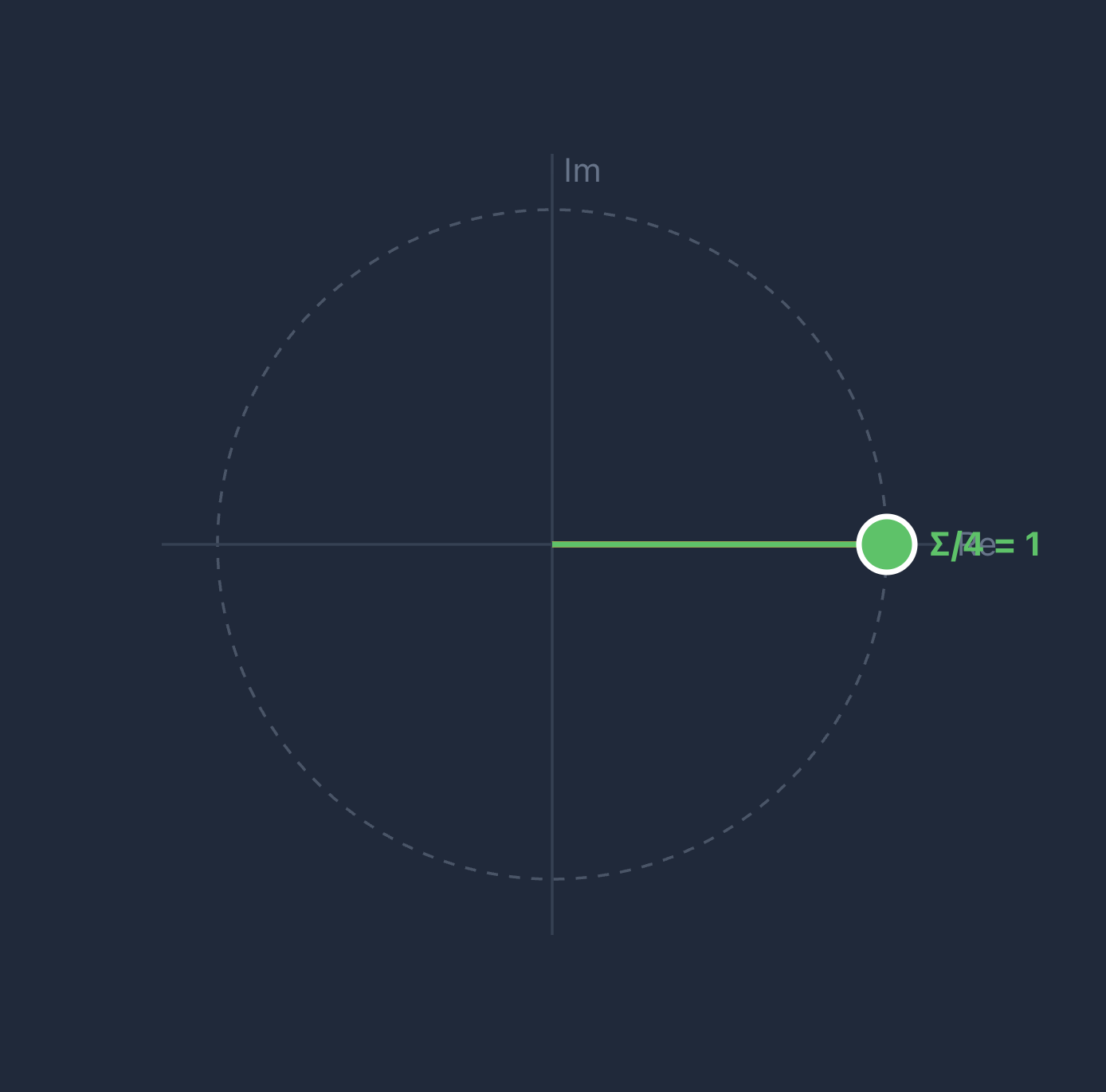
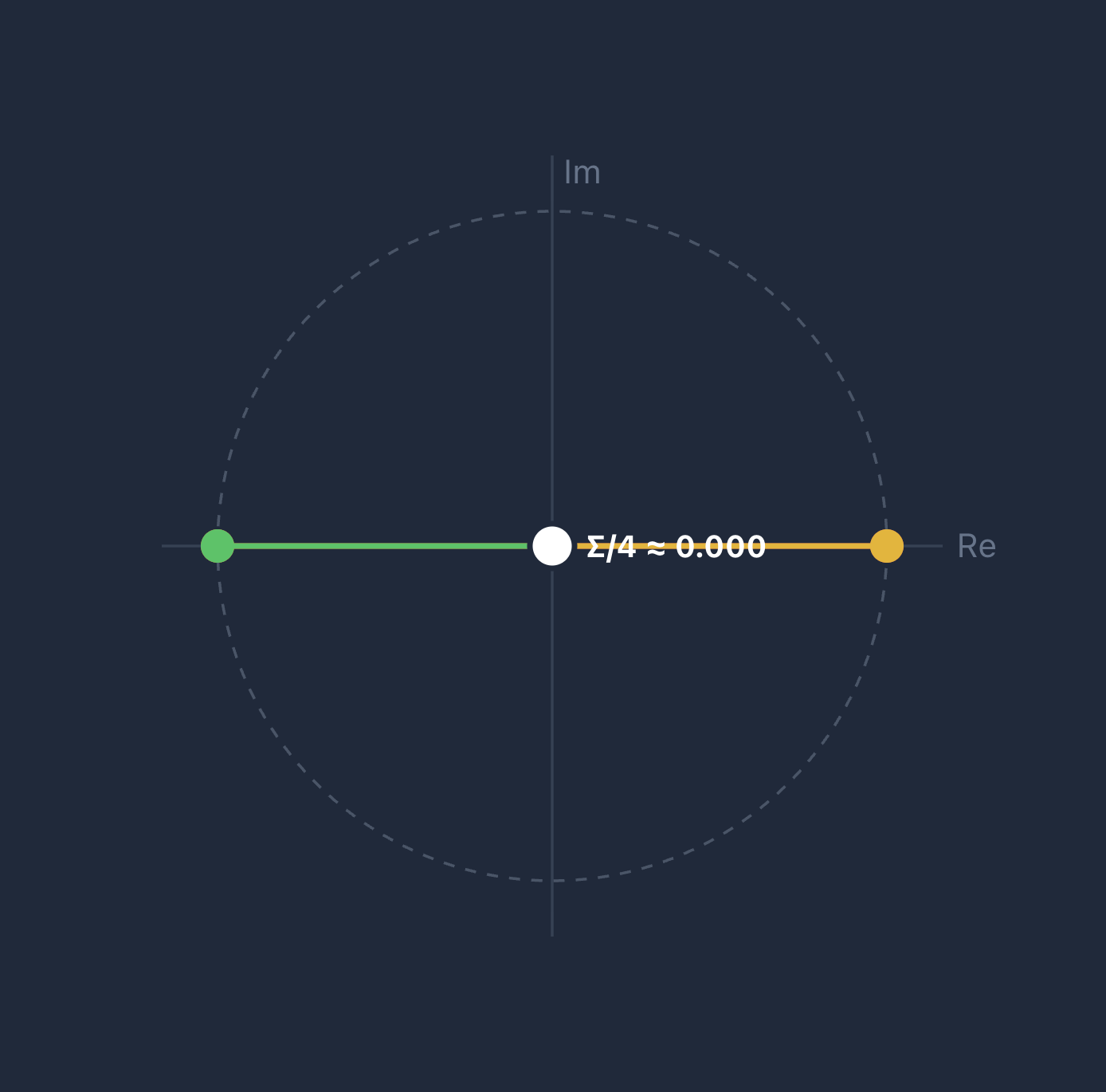
Let's now visualize how Galois automorphisms rotate roots of unity, causing variable terms to cancel.
For a term with , the trace is:
For the constant term (), every . All vectors point to , giving a sum of . This is the message that survives.
When does not divide , the roots are evenly distributed around the unit circle, so their sum is — this is the destructive interference that cancels the garbage. For example, with and , each root gives . These 4 points are evenly distributed around the circle, so their sum = 0.
To summarize, the Field Trace essentially asks: "What part of this polynomial is true from all perspectives?"
- The variable terms are only "true" from specific angles, so they cancel out when you average over all angles.
- The constant term is true from all angles, so it survives and amplifies.
This effectively projects the complex, multi-dimensional polynomial down to its single, stable scalar component (the LWE message).
Trace Algorithm
Computing the trace directly by summing automorphisms (for each term ) would require . Instead, we use a recursive approach that requires only steps.
Definitions
Before running the algorithm, let's define the "ingredients":
- (Dimension): The size of the polynomial ring (e.g., 4096 or 8192). It represents the total number of coefficients in our polynomial.
- (Modulus): The large integer that defines the "clock" for our arithmetic (we calculate modulo ).
- (Ciphertext): A pair of polynomials representing encrypted data.
- Embedded LWE: A specific ciphertext where the message is hidden in the constant term (coefficient of ), and all other coefficients contain garbage that we need to zero out.
- (Automorphism/Rotation): The automorphism , which permutes the coefficients of the polynomial. Think of it as "spinning" the polynomial by index .
- (Rotation Index): An integer that tells the Automorphism function how much to spin the polynomial at step .
- (Decomposition Dimension): The number of digits in the gadget decomposition from key-switching, typically where is the gadget base.
- : Applies the automorphism to the ciphertext. Internally, this requires key-switching (see previous article) to re-encrypt under the original key after rotating.
Intuition: Divide and Conquer
To understand why the trace algorithm is fast, compare the Naive Approach vs. the Recursive Approach.
The Goal: We have 1 good term (Constant) and bad terms (Garbage). We want to sum different "views" (rotations) of the ciphertext so that the bad terms cancel out to zero.
The Naive Approach (Linear)
Imagine trying to zero out the garbage by targeting every single term individually. You would need separate rotations to kill different variable terms.
- Cost: steps. If , that is 4096 operations.
- Complexity: .
The Recursive Approach (Logarithmic)
Instead of targeting terms one by one, we target half of the remaining terms at every step.
- Perform a rotation that turns all odd powers () negative. When you add this to the original, 50% of the garbage vanishes instantly.
- Perform a rotation that turns half of the remaining even powers () negative. Add it. Now 75% of the garbage is gone.
- Repeat.
- Cost: You only need to halve the pile times to reach 1. If , . You finish in 12 steps instead of 4096.
- Complexity: .
The Algorithm
Input: (Embedded LWE)
Loop: For to :
Why these rotation indices?
The index is engineered so that half the surviving coefficients at iteration land in positions where kicks in, flipping their signs.
Adding cancels these flipped terms.
The "+1" ensures is odd — a requirement for valid automorphisms in the cyclotomic ring.
Output:
Complexity:
- This approach requires evaluating automorphisms
- Each automorphism evaluation costs due to key-switching (with gadget digits) and NTT operations
- Total Operations:
Summary
The LWE-to-RLWE conversion uses polynomial embedding followed by the Field Trace operation to project an embedded LWE ciphertext onto a clean RLWE encryption of the original scalar message. The recursive trace algorithm makes this conversion practical, requiring only automorphism evaluations instead of .